Trezor Login — Gateway to Secure Crypto Access
Explore how the Trezor Login process empowers users to access, control, and protect their digital assets with industry-leading hardware security.
What is Trezor Login?
The Trezor Login is not just another username-password gateway. It’s a cryptographic authentication process that leverages the physical Trezor device to verify your identity. When you connect your hardware wallet via Trezor Suite or a Web3 wallet, the private keys remain isolated inside the device — ensuring your assets are safe even if your computer is compromised.
Unlike cloud-based authentication, Trezor Login is decentralized and self-custodial. You, and only you, hold the keys — both figuratively and literally.
Quick Highlights
- 100% device-based authentication
- No usernames or stored passwords
- PIN and passphrase protection
- Compatible with Trezor Suite and Web3 apps
- Offline key management
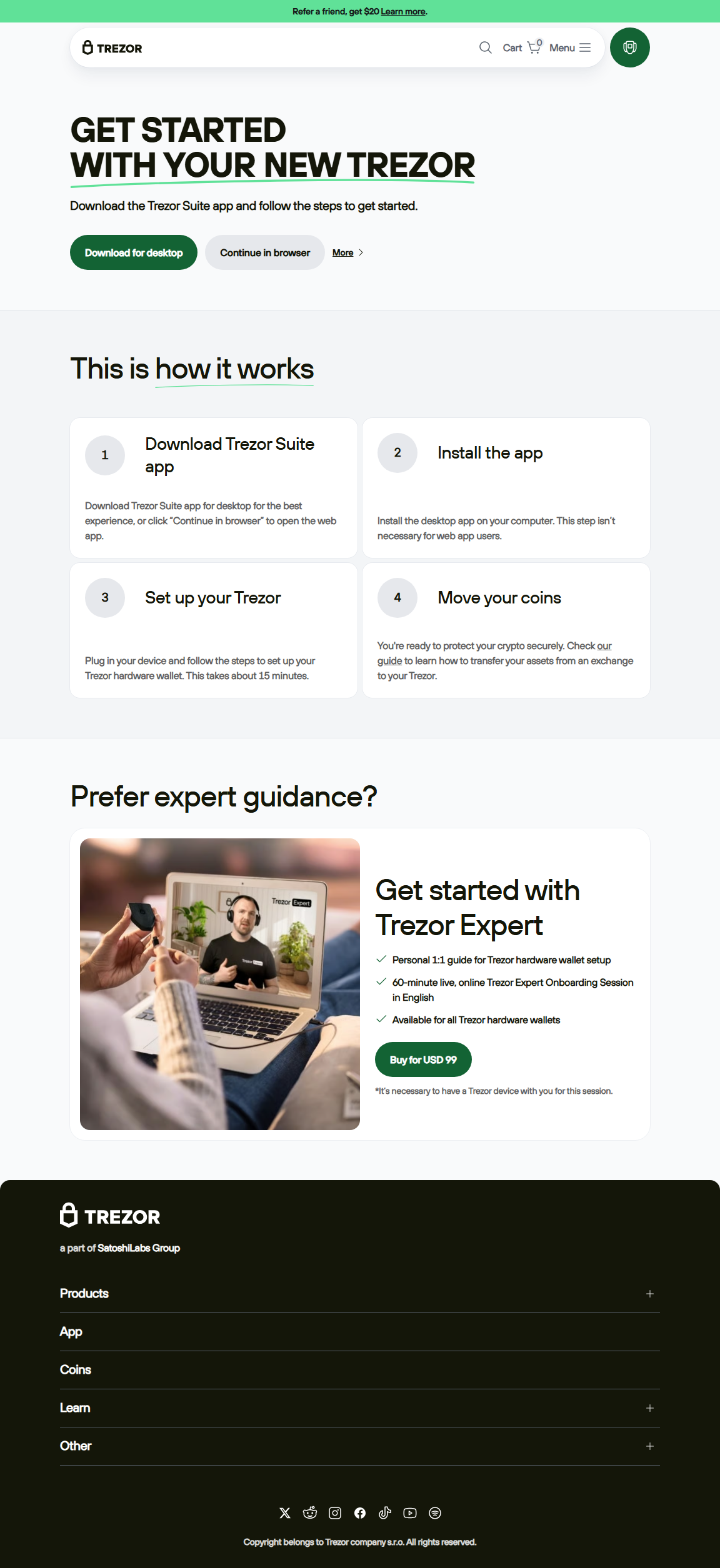
How to Log in with Trezor — Step-by-Step
- Step 1: Download and open Trezor Suite on your desktop or laptop. Ensure it’s from the official Trezor.io website.
- Step 2: Connect your Trezor hardware wallet via USB. Wait until the app detects your device.
- Step 3: Enter your PIN directly on the device’s screen — never on your computer keyboard.
- Step 4: (Optional) Enter a passphrase if you’ve set one up for hidden wallets.
- Step 5: Once authenticated, you’ll see your accounts, balances, and portfolio dashboard. You can now send, receive, or manage crypto assets safely.
Why Hardware-Based Login Matters
Hardware wallets like Trezor act as your personal vault. During login or transaction signing, the cryptographic keys never leave the device. The operation happens inside a secure chip, meaning malware on your computer can’t intercept your private data.
“Trezor Login transforms access control — from passwords you must remember to keys you physically own.”
This concept of “ownership through possession” is at the heart of Web3 and decentralized finance.
Trezor Login vs. Exchange Login
| Feature | Trezor Login | Exchange Login |
|---|---|---|
| Authentication Type | Device-based (PIN + Passphrase) | Username + Password + 2FA |
| Private Key Ownership | User-controlled | Custodial (exchange-controlled) |
| Security Layer | Hardware-enforced cryptography | Server-based protection |
| Accessibility | Requires device connection | Online access only |
Troubleshooting Login Problems
- Device not detected: Reconnect your USB cable or update Trezor Bridge.
- Wrong PIN: Double-check your entry pattern. Ten failed attempts will reset the device.
- Browser issues: Clear cache or use Trezor Suite instead of a web wallet.
- Firmware out of date: Update it through the official Trezor Suite only.
Advanced Security Features
Trezor’s login framework includes multi-layer protection mechanisms:
- PIN Matrix: The randomized grid ensures no keylogger can guess your PIN.
- Passphrase Wallets: Each unique phrase generates a hidden account layer.
- Firmware Verification: Devices verify signed firmware during boot to prevent tampering.
- Secure Bootloader: Prevents unverified code execution.
Frequently Asked Questions
Q1: Can I log in to Trezor without the hardware device?
A: No. You must physically have the device and enter the correct PIN.
Q2: What happens if I lose my Trezor?
A: You can recover all wallets on a new device using your 12/24-word recovery seed.
Q3: Is it safe to use Trezor on shared computers?
A: Avoid it if possible. Even though the private keys remain secure, the environment may be risky.
Trezor Login: Simplicity Meets Absolute Security
With each login, you reaffirm control over your wealth — independent, offline, and invulnerable to centralized breaches. Stay secure, stay sovereign.